Threat Hunting: Get Started
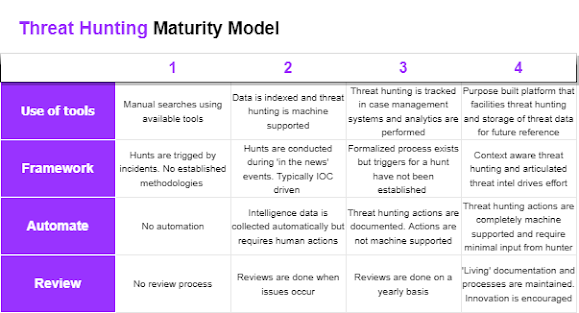
Introduction Threat hunting (detecting and finding things that you weren't previously aware of) has been around for a long time and most 'medium maturity' organizations will attempt to set up some form of threat-hunting activity or program but will find themselves stuck thinking about all the super cool advanced stuff and end up not actually really doing anything at all. So, I've created this blog post to help get people on track to actually develop something for their organization. Why bother? You and your organization should be doing threat hunting because at its heart it is just an application of a foundational concept within cybersecurity. Understanding what is going on in your consistency. So, because of this, it's virtually impossible to not receive a return on investment. Start a hunt and find you haven't been collecting logs for the last 6 months? Great! that's a positive output from threat hunting! Start a hunt and find more shadow IT than you can ...