Securing your estate: The First Step
Introduction
A commonly forgotten fact within the cybersecurity industry is that most organizations are not equipped nor have started to form any sort of security program. This is the case for many reasons because most organizations are SMBs so they don't and likely will never have funds to purchase people and technology and the fact that the cybersecurity industry is incredibly toxic for low expertise and or low capability teams as the well of knowledge we all rely on has been poisoned by vendors and 'thought leaders'.
With this in mind, I have created a small resource that will guide you through what you need to do to make a start. This resource won't reference vendors and I will try to avoid specific jargon.
Enumerate
The term 'You can't secure what you don't know' stands strong even to this day and should be your primary focus before you do anything else. Understanding what assets, you have both physically (computer hardware) and logically (applications, services, platforms) will enable you to make decisions like what risks you are exposed to and which are the most severe or where you need to apply security controls. I've included below considerations and advice you should use when tackling this problem.
Internal Assets
Your internal assets are either going to be local to your LAN or spread across the internet regardless they hold a lot of risk as they are primary interfacing points for your users within the business. The first step to enumerating internal assets is to gain an understanding of your network topology and identify choke points in which data from assets flow. For assets local to your LAN this will likely be switches and perimeter firewalls and for assets external to your LAN you will likely find SaaS applications, Corporate VPNs, Directory services (Azure Active Directory) and deployed security technology to be your choke points.
Once you have identified choke points within your network topology, begin documenting what data is available on the assets establishing connections. As an example directory services will likely provide NETBIOS names for your assets and which users are using those assets or where your organization uses a SaaS application you may be able to enumerate where geographically your users exist. Once your data sources are properly articulated you can begin to build an informal image of your estate and from this image you will want to break up your assets into groups, these groups will allow you to focus efforts in the future and reduce management overhead:
- Critical or "Tier 0" assets. These assets are those that are critical to the function of the business or are used by the majority of your user base. These are often assets that hold financial functions, employee databases, directory servers and file servers.
- Site Locations - Group assets by their physical location, not only will this enable you to easily identify where you need to deploy resources too but it will allow you to further categorize your assets.
- Workstations and Servers. These groups are crucial to proper management as they fundamentally exist differently within your estate and therefore have different requirements.
- Network Devices. Your Switches, Firewalls, Routers, Access Points etc are mostly 'hands-off' infrastructure and as such should be grouped separately.
- VIP Assets. Unfortunately, certain users can cause more disruption than others when things go wrong so its important their assets are articulated and grouped away from the rest of the inventory. This allows you to make unique decisions when deploying patches or making general security decisions.
As you progress with your asset inventory and management you can look to collect a plethora of information that will drastically reduce your mean time to resolution when troubleshooting issues. I've collected below a list of data points:
- Operating system name and version
- Previously installed operating system updates with date/time
- Local users
- Installed Applications
- Security Software Status
- Hardware information
- Network interface information
- Uptime
- Critical services health
- Connected peripherals
- Storage information
- Warranty information
When exploring data points to collect from an asset you will want to consider how often do you need that particular data point updated within your inventory. As an example, you will probably want your network adapter information kept much more up-to-date than warranty information. You can use this to reduce the overall noise or load on your infrastructure.
Inventorying your assets needs to be an active perpetual effort and you need to keep in mind its importance as such getting top-down investment from stakeholders is mandatory for any good asset management program.
People
Unfortunately, it is imperative to understand who your users are, what their roles entail and subsequently what risks they may pose to your estate. This will typically require at least some collaboration with the Human Resources department to create a database of people's names, roles, risk categories and assets assigned to them. Fortunately however if the database doesn't already exist Human Resources will likely be significantly invested in helping you develop one so collaboration is key.
Access Controls
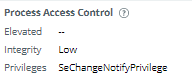
Once you have established your physical and non-physical assets and people you will want to start gaining an understanding of what has access where. This is where your previous work can really shine because with an asset inventory, you can start exploring where business processes exist. Like the prior points this again is a collaborative effort as you need to sit down with all your different teams and just list all the tasks they do. Once you have that list you can start to map out how those tasks correlate to access and then subsequently how you can audit that access.
If your using Active Directory this is particularly easy as where it applies access controls and how is well documented. Regardless of the technology you just need to gain an understanding of what people have access to and document it accordingly. One way to begin documenting your access controls is to start from the perspective of your data. Begin categorizing all the different data types you have whether it is financial, production or client data and just list next to those data types who has access (there's a feedback loop here into your asset groups). This information is super important for decisions you will most definitely need to make in the future particularly when you begin to look to reduce the level of access people have.
Services
Every organization illicits services from other entities and it's important these are documented as they can often exist isolated from the general business ecosystem. A prime example of this is door maintenance and controls. Most organizations just let door maintenance technicians wander around, install new infrastructure (even little desktops) and in general introduce new risks that are not documented. One of the best ways to capture services your company uses is through the finances team as they should who they are paying money to categorise if they don't look to leverage your previous enumeration work around identities and access controls and question any accounts your not familiar with. This will typically open a huge can of worms because its not something people think about at all.
From my experience support contracts for technologies deployed in the business should be a primary focus here because the users and stakeholders view the third-party support teams as a trusted authority on matters and will happily let them remote onto devices to make changes or hand over credentials without thought. So ensure you enumerate all the support contracts that exist in the business, what work they have done in the past and how they are expected to provide support in the future.
Networks
Gaining a strong understanding of your network topology with enable you to make informed decisions on a plethora of cybersecurity topics in the future. You will want to develop specific illustrations for these decisions:
- Architectural overview of how your switches and routing devices direct the flow of traffic
- Flow Diagram of how traffic from an endpoint reaches the internet
- Flow Diagram of how traffic from servers reaches the internet
- Flow Diagram of how traffic from servers reaches endpoints
- Any North-South (External to Internal) topology (such as VPNs)
Quick Wins
- • Identify and leverage bottlenecks in your network infrastructure to scan for assets across all your IP ranges
- Utilize powershell and Windows Management Instrumentation to collect key data points at scale.
- Integrate your asset management system into business processes such as asset deployment and procurement to avoid unknowns creeping up on you again.
- Group and categorize assets based on defined criteria and use cases for easier management.
- Explore the technology already deployed in your estate for opportunities to collect data.
I'm going to be slowly uploading my enumeration scripts to my GitHub here https://github.com/QueenSquishy. Lots of what I've written here is from many hours of work and problem solving things people said couldn't be done because of the complexity but those that have the motivation will find asset management and general enumeration work very rewarding.